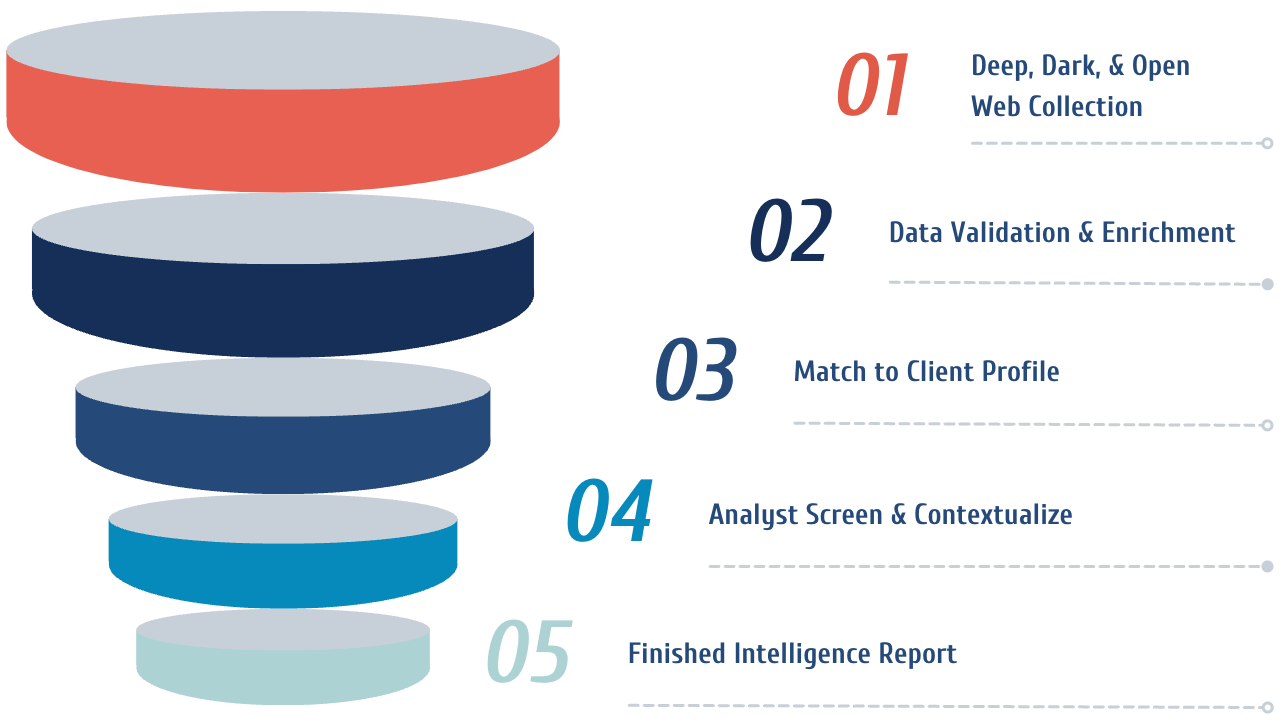
Automated Collection
Tracelight ingests over 500 OSINT sources and covers all major and minor social media networks for complete open web coverage.
Extensive Database
Tracelight has the world's largest breach database, containing over 14 billion records, enabling us to prevent cyber attacks that use breached credentials.
Adversary Engagement
GroupSense is one of the few vendors that still communicates directly with threat actors using over 1,000 carefully crafted and maintained personas, providing unprecedented protection across the dark web.
Linguistic Agility
Tracelight ingests and processes all languages. Our analyst team speaks 7 languages, allowing us to effectively respond to threat actors' messages in their native tongue, reducing translation-related errors.