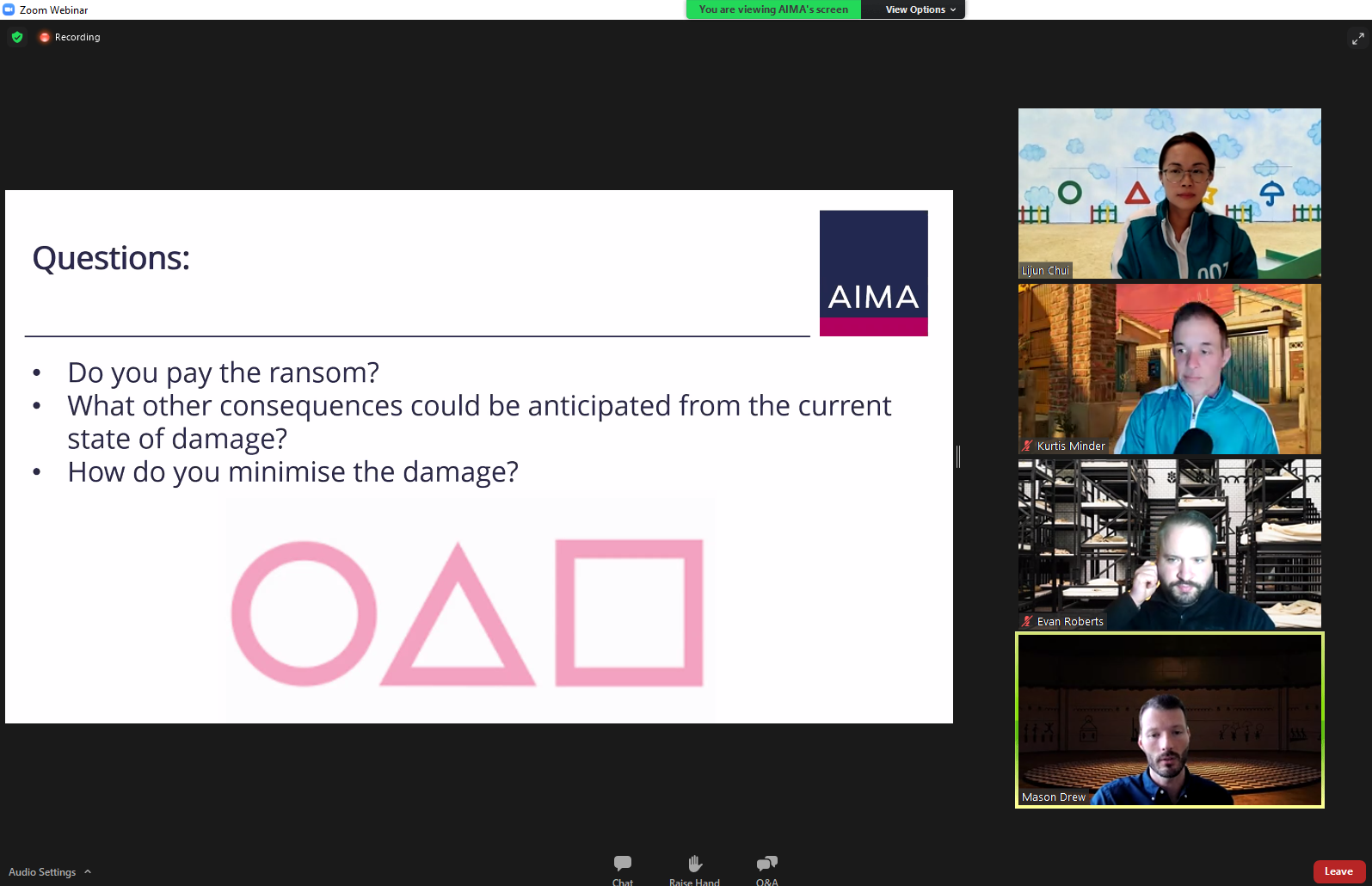
Earlier this week, GroupSense's CEO, Kurtis Minder, participated in *AIMA's APAC Webinar: Cyber Security x Ransomware: Squid Games Edition.
*Note: An account is needed to view the replay.
Like the players in Squid Game, organizations responding to a ransomware incident must make many (“live-or-die”) difficult bet-the-firm decisions often with little reaction time, which have long term ramifications and significant impact. There are times when you feel you’re stepping on a glass bridge where a wrong step could mean death (of critical stakeholder relationships such as investors, regulators or law enforcement agencies).
About the Squid Games Cyber Drill:
Kurtis and a handful of top-rated cyber security panelists participated in a cyber drill mimicking a ransomware attack.
- A simulated security event which escalated into a crisis level event
- Multi-jurisdictional reporting decisions
- Negotiation with a ransomware attacker
The event was moderated by Kher Sheng Lee, Managing Director, Co-Head of APAC and Deputy Global Head of Government Affairs, AIMA. It included panelists from Bird & Bird, FTI Consulting and GroupSense.
First Steps After a Ransomware Attack
During the drill, Kurtis was asked about first steps you should take after a ransomware attack. "There are a lot of things you need to do in advance of talking to the threat actors. We often get pulled in after the attack. However, it is better to engage earlier. Ransomware is fundamentally different than a typical cyber-attack. Knowing your incident plan is so important," says Kurtis Minder, GroupSense CEO.
Should the victim involve law enforcement? The panel discussed this topic in great detail. It is mostly up to the business on whether or not engage law enforcement. However, the panel all agreed it is a best practice to involve law enforcement. Law enforcement, such as the FBI, takes inventory of ransomware attacks. They can also provide useful information which might be beneficial during a negotiation.
To Pay the Ransom, or Not to Pay the Ransom, That is the Question
The question on everyone's mind was, "do I pay the ransom or not pay the ransom?" According to Kurtis, "it depends." If you can restore and recover your data – the best thing to do is to not pay the ransom. But it might not be possible. For example, if you are a healthcare organization, you might be talking about the loss of lives. So many cases are different. So many factors come into play.
"When communicating the event to your employees, customers, board – the instructions I give is to communicate as transparently as possible within your knowledge boundary. Ideally you want to engage the threat actors at some point to buy yourself time. Do you pay the ransom or not? It comes down to the business impact and how long you would be down and what that looks like for your business," says Kurtis Minder, CEO at GroupSense.
How to Protect Your Organization
The AIMA cyber drill wrapped up by asking the panelists for last thoughts on how to protect yourself from a ransomware incident. Kurtis commented, "I hope that ransomware negotiation isn’t a career for people. I want organizations to stop it before it happens. Many of the cases that we work are preventable. Basic cyber hygiene isn’t complicated that can reduce your likelihood of being a victim by 90%. Ransomware attacks are opportunistic in nature. Have an incident response plan and practice that plan. Have someone to advise you on the ransomware scenario – you need to have a good sounding board."
About Kurtis Minder:
 Kurtis Minder is the CEO and co-founder of GroupSense, a leading provider in Digital Risk solutions. Kurtis built a robust cyber reconnaissance operation protecting some of the largest enterprises and government organizations. Kurtis has been the lead negotiator at GroupSense for ransomware response cases. He has successfully navigated and negotiated some of the largest ransomware, breach, and data extortion cases world-wide. With over 20 years in the information security industry, Kurtis brings a unique blend of technical, sales and executive acumen.
Kurtis Minder is the CEO and co-founder of GroupSense, a leading provider in Digital Risk solutions. Kurtis built a robust cyber reconnaissance operation protecting some of the largest enterprises and government organizations. Kurtis has been the lead negotiator at GroupSense for ransomware response cases. He has successfully navigated and negotiated some of the largest ransomware, breach, and data extortion cases world-wide. With over 20 years in the information security industry, Kurtis brings a unique blend of technical, sales and executive acumen.
About AIMA
AIMA draws upon the expertise and diversity of its membership to provide leadership in industry initiatives such as advocacy, policy and regulatory engagement, educational programmes and sound practice guides. AIMA works to raise media and public awareness of the value of the industry.
AIMA set up the Alternative Credit Council (ACC) to help firms focused in the private credit and direct lending space. The ACC currently represents 200 members that manage US$450 billion of private credit assets globally.
AIMA is committed to developing skills and education standards and is a co-founder of the Chartered Alternative Investment Analyst designation (CAIA) – the first and only specialised educational standard for alternative investment specialists. AIMA is governed by its Council (Board of Directors).






