This week, Senior Threat Intelligence Analyst Samira Pakmehr and Director of Intelligence Operations Bryce Webster-Jacobsen presented their talk, "The Role of Cryptocurrency in Ransomware Negotiations and Other Cybercrimes," at the virtual SANS Ransomware Summit. Packed with a full day of sessions, attendees come away from the summit with deeper insight into today's ransomware landscape and its inner workings.
During their session, Bryce and Samira looked deeper into how cybercriminals use cryptocurrency in ransomware negotiations and how threat actors avoid detection. Bryce and Samira also explained the following in more depth:
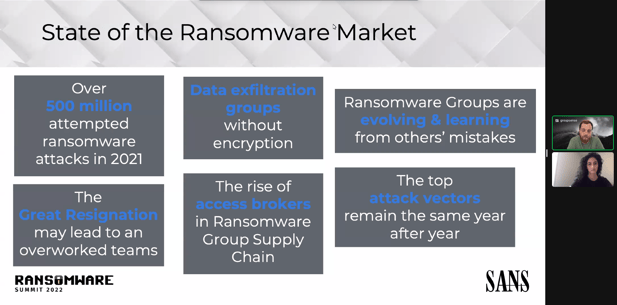
- The state of the ransomware market: the top attack vectors, the evolution of ransomware groups, increase in initial access brokers, and more
- Why and how compliance can affect cryptocurrency transactions and what future regulations might look like, including SUEX Binance
- How threat actor evasion methods such as privacy coins, mixing/tumbling, gift cards, and other laundering tools can affect transactions
- What types of detection methods exist: namely, transaction monitoring and know your customer (KYC) and how best to implement them
During a lively Q&A session, Samira and Bryce told the audience they believe that cryptocurrency isn't going anywhere. As detection methods, tracking, and seizure get more complex, Samira hypothesized that ransomware gangs would use money couriers to obfuscate their identities further, ultimately challenging law enforcement.
As cryptocurrency regulations continue to change in each country, we will have to wait and see what the future holds for cybercriminals using different coins. And it's not just the cyber underground that analysts will be keeping their eyes on—the metaverse will potentially be a new avenue for threat actors to do their dirty work in.
For more information on GroupSense's Ransomware Negotiation Services, click here.