Ransomware attacks have exploded over the past few years, and ransomware groups have reinvested their earnings into their malicious businesses.
Threat actor groups have discovered a significant opportunity within the market to provide Ransomware-as-a- Service (RaaS). Much like the Software-as-a-Service (SaaS) offerings we are all familiar with, RaaS operations have employees, customer service, and a business structure to lean on. It paves the way for inexperienced threat actors to utilize the expertise of more advanced threat groups, ultimately expanding the effects of ransomware to a broader breadth of targets.
One RaaS group, Conti, became prolific over the last several years, with attack numbers above 1,000. The ransomware group is having a pretty bad month. After aligning themselves with Putin’s invasion of Ukraine, assumed Ukrainian members took the liberty of leaking months’ worth of internal chat logs and documents, revealing their internal business structure, office politics, and pay scales. GroupSense analysts have been translating and digesting the information, corroborating the intelligence with data that they have already collected on Conti through threat investigations.
Conti
Conti has successfully targeted and impacted significant players from the financial sector to the software industry, such as the Japanese electronics supplier JVCKenwood, London-based high society jeweler Graff, and the Irish health system. Last year, GroupSense threat analysts observed Conti’s tactics, techniques, and procedures (TTPs) when the group breached a client’s network and demanded ransom.
In a recent chat log leak, GroupSense learned that Conti has upper and middle management with entry-level employees that do the leg work. The separation of roles within Conti enables the employees to focus on specific parts of the cyber kill chain. Gaining initial access to the system is the most time-consuming part of the attack. It requires reconnaissance and planning, which “initial access brokers” work on over weekends. This leg work allows for more attacks and ultimately more revenue for the ransomware group.
Conti typically deploys their ransomware through targeted spear-phishing and broader phishing campaigns that contain malicious attachments or links. The attachments serve as vessels for deploying other malware that utilizes more advanced techniques. These vessels are typically called “loaders” or “downloaders,” and they will do their best to mask the actual malware such as TrickBot, or in this case, Conti ransomware.
When our client was hit with Conti last year, they hired GroupSense for our Ransomware Negotiation Services. As part of the service, GroupSense confirms that the actor returns the decrypted data before the client pays the ransom. After providing sufficient proof that the actor returned the data, our negotiator helped our client pay the ransom. Unfortunately, the story doesn’t end here.
Conti Again?
Months later, the client’s customers started receiving phishing emails on the same thread that Conti used to communicate with the client, meaning the actor had access to the old email thread. This method, called email chain hijacking, allows the threat actor(s) to send phishing emails by replying to old email threads, which tricks victims into thinking the email is
legitimate. Access to the original email thread strongly indicates that Conti could be behind a repeat attack.
The phishing emails were riddled with typos, grammar mistakes and had other pronounced signs of phishing, including mismatched sender names and addresses with a badly spoofed email domain. Typically, when Conti uses phishing as a vector, they are careful to cover their tracks and make the email look as legitimate as possible. Email chain hijacking increases the likelihood of success for phishers. Furthermore, Conti was not known to use email chain hijacking in previous attacks. With these conflicting pieces of evidence, our analyst dove deeper to find out if the phishing attack was coming from Conti or a second and unrelated actor.
Connecting the Bots
 The GroupSense analyst started an investigation to compile a list of threat actors who had
The GroupSense analyst started an investigation to compile a list of threat actors who had
historically used the email chain hijacking technique within previous campaigns. During this investigation, the analyst identified the following groups:
- TrickBot Gang
- The newly revived Emotet
- TA 551 (Shatak)
- IcedID campaigns
- QakBot campaigns
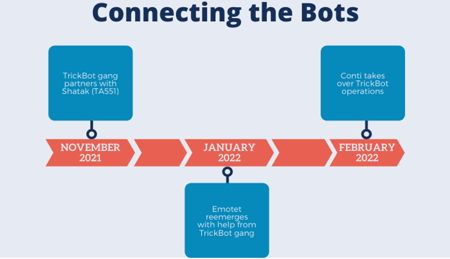
In November 2021, the intelligence community discovered that the TrickBot Gang teamed up
with TA551 to deploy Conti ransomware. In January 2022, SANS found that Emotet had reemerged with help from the TrickBot group. In February 2022, AdvIntel discovered that the Conti group had taken over the TrickBot operations.
Knowing several roads lead back to the Conti Group, the analyst deployed the malicious link in a sandbox environment. The link downloaded several pieces of malware to the device, including the IcedID loader operated by TA 551. GroupSense assessed with high confidence that the Conti ransomware syndicate was actively targeting our client’s customer base using stolen email threads.
Below are the hashes gathered upon detonation and the IP addresses that the payload contacted.
IP Addresses:
- 208.95.112[.]1
- 23.21.43[.]186
- 54.225.179[.]233
- 82.221.103[.]243
| SHA-256 Hashes |
| 00c62ed42795f996b5f963c69ce918c2623d72896ebb628dfd9bc800514900ce |
| 086a7e44de35a235bc258bf1107e22a7dc27932cb4d7e3ebcd1f368acc000caa |
| 0cd5b187ffad353e52c996c8f5bb1f5499d42e3525a56d1787a587a00b67b491 |
| 0f8ced5f44da7acf761d497fbffd203cc8d213d837ca76e0c63d90bf914d2f76 |
| 10d8b828af4080ab9d7a4943a64960bf047637a95ac3aac046b9e7b7232943b6 |
| 31fc706ae4bd5093aecb6a0b7f9d3b686feb284076b1122aaff978779612dc06 |
| 51980490612ad901964738ab28951c55b2140e71e460a43bd4bc3ef80cd626b2 |
| 5a0b7495f961d70b1e9a5a41aaae77748f9fb042110b66ea76ef7c5757e61fa1 |
| 5e872715109b381c99aa19e2435628640505794e09a1998de7b92c2a5aea38e1 |
| 61acd6e7405fad348433f8de4b12ed97b42caccbcf28fe0e4ba4b4a5d2ea707e |
| 68e37eed2e04830fce9f735d8a2ecebb19a651394f5d590581370ac5d7754d90 This one matches a ruleset for the IcedID payload |
| 6b0ceccf0103afd89844761417c1d23acc41f8aebf3b7230765209b61eee5658 |
| 6b88c6ac55bbd6fea0ebe5a760d1ad2cfce251c59d0151a1400701cb927e36ea |
| 6cce352f8426a6cb2d41d5d108658cfa1244f0142d6f60bc96e3c4c2904913c3 |
| aa5daecee872ca7c079b5363c2ffb0a6bbb335414ac3ce2006bc18015fcd45e4 |
| bc05a98d03525d3255d0e2d55edd6afb93e4b5ef7db2ff17609b541a5fce3d7d |
| bdd5111162a6fa25682e18fa74e37e676d49cafcb5b7207e98e5256d1ef0d003 |
| d1b9d32702d7d7a184ab4654c204e6d385a9499fde63e0b06bda60f8077a7862 |
| dfc98ccf84f4551aae0f4ac0334df103e2cfeb7a55af486b68c0392fc78a5fa4 |
| e39d6a57d2f16e60c4075d07741dadd6a2742a85aceb250083d7ab103279f737 |
| e5a870dda2bca2b632f9aa3eee7768b5dd1498046d53af5fb6b5d5920debe27a |
| f6006f75b9c9f94761370e6810cdf9bc1d2794f7a3513a9bfe119606d76d2992 |
| 261fcca4a1177c03c7aff8b3bcdbf4016c2a3da6674e6afb4c8a885d9784064b |
Repeat Attacks
It’s rare for ransomware groups to attack the same target twice. Because RaaS groups run like businesses, they work on similar reputational rules as legitimate companies. If a RaaS group says they will return stolen data from their victims, they are expected to keep their word. If they return the data to the victims, they can only cash out on the data once.
In this case, Conti was trying to cash out twice on the same set of stolen data. Our analysts have not seen such a brazen attack that would damage a threat actor’s reputation before.
Wider Implications
This investigation suggests that the Conti ransomware syndicate is rapidly increasing its sophistication and standing in the initial access ecosystem. This increased sophistication means that they can hit larger, more complex systems and demand even higher ransoms in the future.





