 Recently Bryce Webster-Jacobsen, Director of Intelligence Operations at GroupSense, joined Bace Cybersecurity Institute for a webinar on Cryptocurrency and Security. The webinar walked through cryptocurrencies and the promise it delivers as a secure and efficient anonymous monetary transaction.
Recently Bryce Webster-Jacobsen, Director of Intelligence Operations at GroupSense, joined Bace Cybersecurity Institute for a webinar on Cryptocurrency and Security. The webinar walked through cryptocurrencies and the promise it delivers as a secure and efficient anonymous monetary transaction.
Bryce and David Rosenthal, formerly at Sun Microsystems and Nvidia, discussed:
- Does it actually fulfill these promises?
- What about their use in ransomware?
- Is it really easy to acquire cryptocurrencies to pay a ransomware ransom?
- What are the social and environmental effects of cryptocurrencies?
If you missed the live event, no worries, you can catch the on-demand replay here. Below are a few highlights from the discussion.
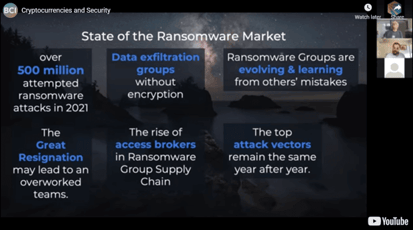
According to Bryce, three common ways crypto is used is in: ransomware operations, day-to-day dark web transactions, and the purchase data through other “non-traditional” communications channels, which Bryce is classifying as communication channels outside of the dark web (i.e. a discord server, telegram channel, etc.,) Cryptocurrencies are not the only way for exchanges, but they are the primary tool used for these exchanges.
Bitcoin, Monero, and Alt-Coins are the three preferred cryptocurrencies for the cyber underground. Bitcoin is the most widely accepted and used, however, it has some privacy concerns due to traceability. Monero is occasionally used and some ransomware operators prefer XMR. Alt-Coins are not commonly used.
As far as ransomware operators, they always demand ransom payments in cryptocurrency and typically a disposable wallet is used. Because of this, corporate ransomware victims may face difficulties obtaining large cryptocurrency sums. The crypto is laundered after the transaction.
Watch the full on-demand webinar here >
About Bace Cybersecurity Institute
The Bace Cybersecurity Institute was founded as an outgrowth of an industry initiative spearheaded by the late Rebecca (Becky) Bace. The “Critters” group brought together a carefully curated group of cybersecurity and business executives to take a closer look at the changes necessary to create a more secure cyber world. Over the years, the founding “Critters” members invited additional members to help expand our perspective and extend our reach. With the passing of Becky, we have launched the Bace Cybersecurity Institute to honor Becky’s memory and contribution to the cybersecurity industry and to continue the good work she launched with the Critters initiative. Visit their website: https://www.bacesecurity.org/
About Bryce Webster-Jacobsen
 Bryce is the Director of Intelligence Operations at GroupSense, a leading provider in Digital Risk solutions. Bryce leads the day-to-day intelligence activities of GroupSense's Analyst and Research teams producing finished, tailored intelligence for our diverse clients.
Bryce is the Director of Intelligence Operations at GroupSense, a leading provider in Digital Risk solutions. Bryce leads the day-to-day intelligence activities of GroupSense's Analyst and Research teams producing finished, tailored intelligence for our diverse clients.
Prior to GroupSense, Bryce worked in strategic international education initiatives while pursuing OSINT training and investigations, primarily focused on studying extremist movements, as a passion project.