We all have a role in its prevention
Each member of our community has the ability and responsibility to limit the spread of disinformation that can potentially impact our elections as well as other important issues for our state. In the following guide, you will learn more about what disinformation is, how to spot it, and how you can help prevent the spread of disinformation.
Understanding disinformation:
Disinformation is the spread of heavily biased and untrue information. As our lives continue to move into the digital space, social media is frequently used to spread disinformation. It is a common misconception that these campaigns target political candidates, but in reality, they target voters, seeking to create distrust and chaos. Disinformation targets more than our elections - we have seen disinformation on other topics like Net Neutrality, whether to vaccinate children, and other important, yet polarizing, issues.
Everyone can take steps to prevent the spread of disinformation. In this guide, you will learn:
- Social media’s role in the spread of disinformation
- How to prevent your social media feeds from becoming biased
- How to identify fake social media accounts
- Tips for validating the credibility of information you find online
- Fact checking online news sources
- Validating the authenticity of images and videos
- Things you can do to prevent the spread of disinformation
- How to prevent your accounts from being used to distribute disinformation
- How to report suspected disinformation online
Social media’s role in the spread of disinformation
How to prevent your social media feeds from becoming biased [1]
Social media feeds use algorithms that are intended to provide information you are likely to have an interest in based on how you have interacted with information online in the past. As a result, your news feeds can become biased and distorted.
Train your newsfeed
You can train your newsfeed to deliver a more balanced set of information by intentionally seeking out different points of view from reputable sources. By doing this, you can understand all sides of an issue, and more easily spot disinformation.
How to identify fake social media accounts
When accepting new friend / follow requests, be on the lookout for duplicate accounts.
When following accounts, consider factors like:
- How old is the account?
- How many followers, connections, or friends do they have?
- Who do they follow?
Tips for validating the credibility of information you find online
On Twitter, lies are 70% more likely to be retweeted than facts. [2]
The information age has quickly become the disinformation age. Here are a few tips to help you get a handle on fact vs. fiction vs. a stretched truth:
Fact-checking online news sources
Take time to evaluate stories you are reading, including understanding the website or organization presenting the story, and make sure the information is current and accurate. Here are a few simple questions you should ask to verify the validity of a piece of news online:
- Is the source (publication and author) of the article reputable?
- Is the evidence used as the basis of the argument from a cited source that is credible?
- Is the main conclusion of the article supported by the evidence [3]?
- Is the publication date current? Frequently, outdated stories will pop up on social media and be shared as if they are related to a current news event in an attempt to deceive people and shape their opinions.
- Double-check any questionable content on snopes.com or factcheck.org
Validating the authenticity of images and videos:
Be on the lookout for images and videos that have been modified or edited to present a distorted message. So called “deepfakes”, or videos that contain the face of one individual superimposed onto the body of someone else, are becoming increasingly prevalent on social media.
- Use Google image search to search by file name or URL to verify the image you are about is original, authentic, and free of deceptive editing.
- Identify deepfakes by looking for face discolorations, unnatural lighting, or blurriness where the face meets the neck [4].
Don’t join the botnet army: Things you can do to prevent the spread of disinformation
Prevent your email and social media accounts from being hijacked
One of the ways disinformation is distributed is by hijacking social media and email accounts, and using those accounts to share disinformation across social platforms and websites [5]. Prevent this by:
- Deleting accounts you no longer use
- Use a unique password for each account you have
- Be cautious about duplicate invites (i.e.: a current friend sending another friend request)
Be a part of the solution:
If you accidentally share fake news, take action to correct it - edit or delete the post. Comment and let people know you’ve shared in error.
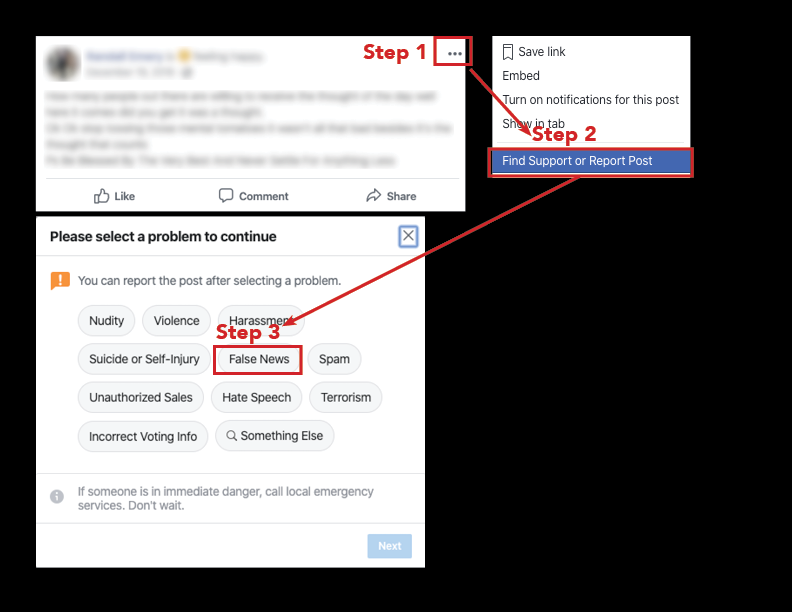
How to report suspected fake news on Facebook:
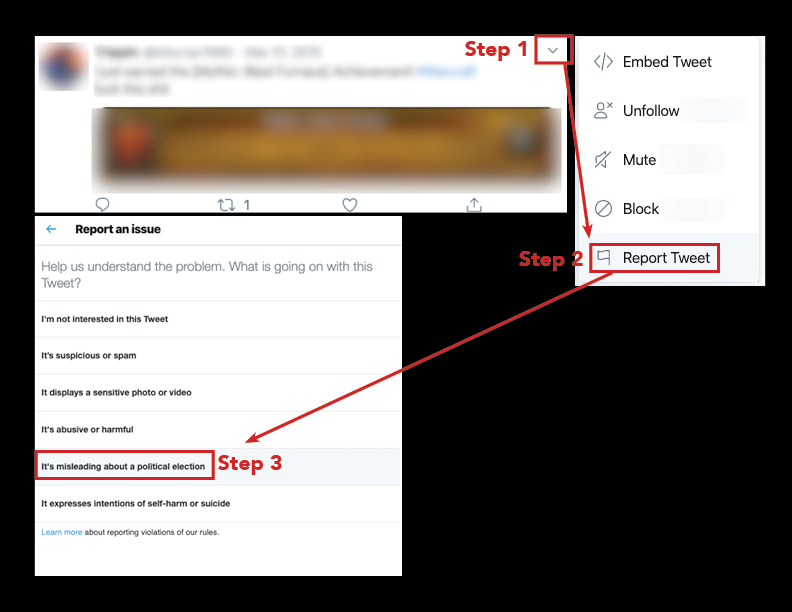
How to report suspected fake news on Twitter:
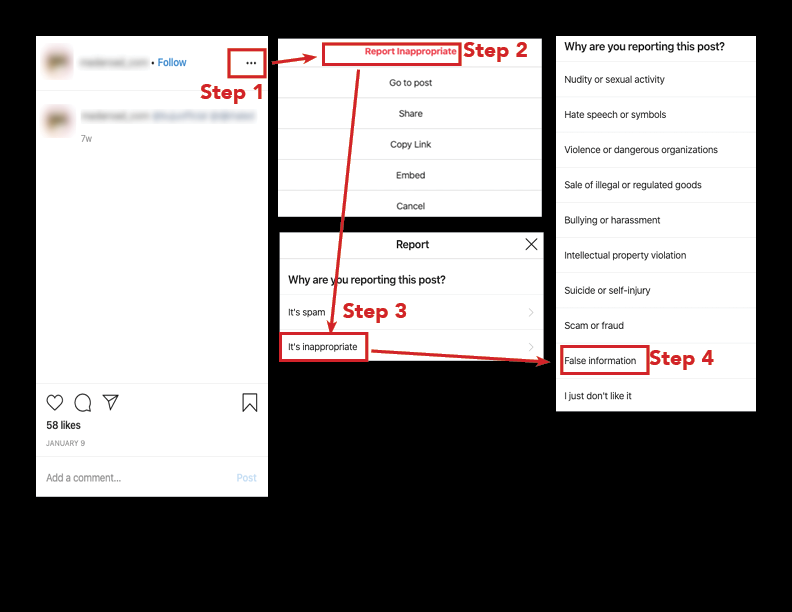
How to report suspected fake news on Instagram:
In the digital age where information of all kinds is so easily created and accessed, it is our collective responsibility to ensure that the information we use and share is true and accurate.
More resources can be found here:
4 steps to stop the spread of disinformation online; Brookings
How to stop the spread of disinformation; Mozilla
How to Spot Fake News; FactCheck.org (Article)
How to Spot Fake News; FactCheck.org (Video)
References
[1] 4 Steps to stop the spread of disinformation online
[2] https://www.theatlantic.com/technology/archive/2018/03/largest-study-ever-fake-news-mit-twitter/555104/
[3] https://www.americanpressinstitute.org/publications/six-critical-questions-can-use-evaluate-media-content/
[4] https://slate.com/technology/2019/06/how-to-spot-deepfake-videos.html
[5] https://usa.kaspersky.com/resource-center/threats/botnet-attacks