Phishing is a cybercrime technique that is used to deceive individuals into providing sensitive information, such as passwords, credit card numbers, or social security numbers, by impersonating a trustworthy entity. This article aims to provide a comprehensive understanding of phishing, how it works, its impact, and most importantly, how to protect yourself from falling victim to these attacks. By familiarizing yourself with the various aspects of phishing and implementing the suggested security measures, you can significantly reduce the risk of becoming a victim.
Understanding Phishing
The Definition of Phishing
Phishing is the act of luring unsuspecting individuals into divulging their personal information through fraudulent means, most commonly via email, phone calls, or instant messages. The perpetrators disguise themselves as legitimate organizations in order to gain the victim's trust and manipulate them into providing sensitive data.
The History of Phishing
Phishing has been a prevalent cyber threat since the mid-1990s when online banking and e-commerce started gaining popularity. The term "phishing" itself emerged from a hacker's shorthand for "fishing," as the perpetrators cast out fraudulent messages and bait unsuspecting victims into taking the bait.
Over the years, phishing attacks have become increasingly sophisticated, making it challenging for individuals to distinguish between legitimate and malicious communication.
Different Types of Phishing Attacks
Phishing attacks come in various forms, each with unique characteristics and objectives. Understanding the types is crucial in recognizing and protecting yourself from potential threats:
- Email Phishing: This is the most common form of phishing, where attackers send fraudulent emails claiming to be from a legitimate source, such as a bank or an e-commerce website. The emails typically contain links or attachments that, when clicked or accessed, prompt the victim to provide sensitive information.
- Spear Phishing: Spear phishing is a more targeted attack, where the perpetrators customize their messages to appear genuine and relevant to a particular individual or organization. By leveraging personal information and context-specific details, attackers increase the likelihood of success.
- Smishing: Smishing involves using SMS or text messages to trick individuals into sharing personal information or clicking on malicious links. These messages often claim that urgent action is required, exploiting the sense of immediacy to bypass the recipient's suspicion.
- Vishing: Vishing attacks rely on voice communication, wherein attackers call individuals, pretend to be from a trustworthy organization, and attempt to extract sensitive information over the phone. They may create a sense of urgency or use social engineering tactics to manipulate victims into revealing their details.
How Phishing Works
The Phishing Process
The phishing process typically involves several steps, which attackers meticulously follow to maximize their chances of success. While the techniques may vary, the underlying objective remains the same: deceive the recipient and obtain their sensitive information.
- Selecting the Target: Attackers identify potential targets based on various factors, including the perceived value of their personal information and the likelihood of a successful phishing attempt.
- Creating Bait: Attackers craft fraudulent messages or communication channels that closely resemble those of legitimate organizations.
- Luring the Victim: By leveraging social engineering techniques or exploiting a sense of urgency, attackers entice the target to click on malicious links or provide their information.
- Acquiring Sensitive Information: Once the victim falls for the trap, their sensitive information, such as passwords or credit card details, is gained by the attackers.
Common Phishing Techniques
Attackers employ a variety of techniques to manipulate their victims. By familiarizing yourself with these techniques, you can enhance your ability to recognize and avoid potential threats:
- Email Spoofing: Attackers forge emails to make them appear as if they were sent from legitimate sources, such as banks or popular websites.
- Malicious Attachments and Links: Attackers often include attachments or hyperlinks that, when clicked or accessed, can lead to malware installation or phishing websites designed to collect information.
- Domain Name Impersonation: By using similar-looking domain names or creating subdomains that closely resemble legitimate websites, attackers trick individuals into thinking they are interacting with trusted organizations.
- Social Engineering: Attackers exploit human psychology and emotions to manipulate victims into providing confidential information or making financial transactions.
Real-life Examples of Phishing
Phishing attacks are constantly evolving, taking advantage of new vulnerabilities and technological advancements. Here are a few notable real-life examples:
Here is an example of a phishing attempt received by one of our employees. Note that the email subject line is asking the victim to perform an urgent action. You can see that the email address does not match the sender.
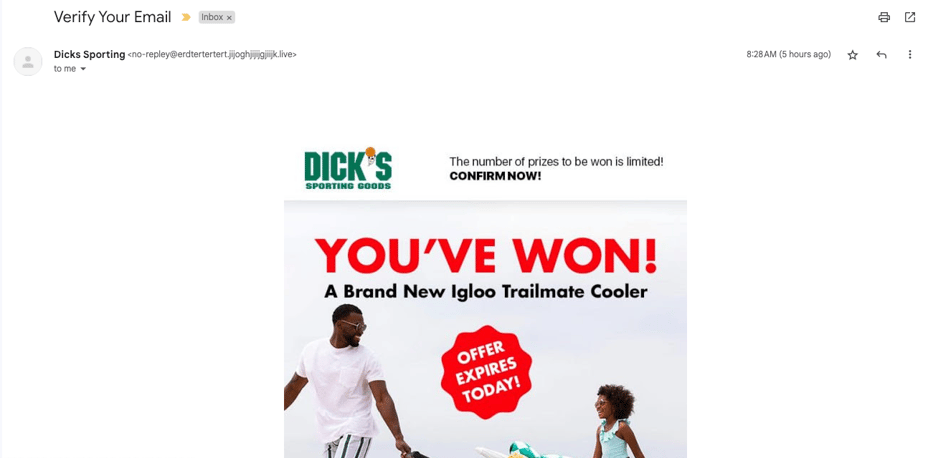
.jpeg?width=211&height=456&name=IMG_2692%20(1).jpeg) Here is another example of a phishing email. The threat actor is urging the victim to take action with an alluring prize.
Here is another example of a phishing email. The threat actor is urging the victim to take action with an alluring prize.
The Impact of Phishing
Personal Consequences of Phishing
Falling victim to a phishing attack can have severe consequences for individuals. Some of the potential personal impacts include:
- Financial Loss: Phishing attacks often lead to unauthorized access to bank accounts and credit card fraud, resulting in substantial financial losses for the victims.
- Identity Theft: The stolen personal information obtained through phishing attacks can be used to perpetrate identity theft, resulting in long-term financial and emotional damage.
- Compromised Online Accounts: Once attackers gain access to an individual's online accounts, they can hijack them for malicious purposes, such as spreading malware or conducting further fraudulent activities.
Business Consequences of Phishing
The impact of phishing is not limited to individuals; it can also have significant implications for businesses:
- Financial Losses: Businesses may suffer financial losses due to unauthorized access to company accounts, payroll fraud, or the cost of mitigating the consequences of a successful phishing attack.
- Reputation Damage: Falling victim to a phishing attack can severely damage a company's reputation, leading to a loss of customer trust and potential business opportunities.
- Data Breaches: Successful phishing attacks can result in the exposure of sensitive customer data or company secrets, leading to legal implications and regulatory fines.
How to Recognize a Phishing Attempt
Red Flags in Phishing Emails
Recognizing phishing attempts is essential in protecting yourself from potential attacks. Here are some red flags to watch out for in phishing emails:
- Generic Greetings: Phishing emails often lack personalization and address recipients with generic greetings like "Dear Customer" instead of using the recipient's name.
- Urgent Language: Attackers use language that creates a sense of urgency or fear, pressuring recipients to act impulsively without considering the authenticity of the message.
- Spelling and Grammar Errors: Phishing emails may contain spelling mistakes, grammatical errors, or awkward sentence structures that are uncommon in legitimate communication.
- Requests for Personal Information: Legitimate organizations rarely request personal information, such as passwords, over email. Be cautious if an email asks you to provide such sensitive details.
Suspicious Links and Attachments
Carefully examining links and attachments in emails is crucial to avoid falling victim to phishing attacks:
- Hover Before Clicking: Hovering your mouse over a link without clicking can reveal the actual destination URL. Ensure that the URL matches the claimed source.
- Verify File Extensions: Be cautious when opening attachments, especially those with executable file extensions like .exe or .bat, as they are often used to spread malware.
- Don't Trust Unfamiliar Email Senders: If you receive an email from an unfamiliar sender, exercise caution before clicking any links or downloading any attachments.
Urgent Requests for Personal Information
Be wary of any request, especially those regarding personal or financial information, that demands an immediate response. Legitimate organizations generally provide avenues for securely submitting sensitive information, rather than relying solely on email communication.
Remember, staying vigilant and adopting a skeptical mindset while assessing emails and online communication is key to avoiding phishing attempts.
By understanding the definition, techniques, and impact of phishing, as well as learning how to recognize and protect yourself from these attacks, you can maintain a stronger defense against this pervasive cyber threat. Stay informed, follow best security practices, and spread awareness to help create a safer online environment for everyone.
One of the best ways to stay ahead of attack vectors like phishing is to read our guide, "Protecting Your Organization From Cyber Incidents." You will learn practical tips to implement that will improve your organization's cybersecurity posture, including technical and business tips.




